Rotating your SSL/TLS certificate
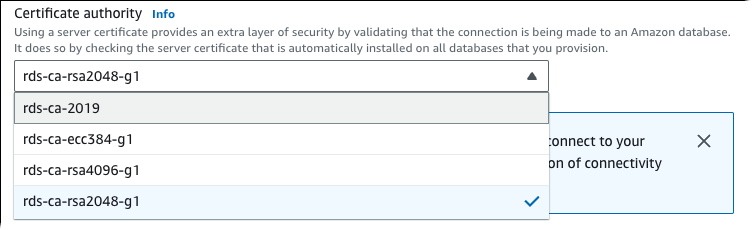
Amazon RDS Certificate Authority certificates rds-ca-2019 expired in August, 2024. If you use or plan to use Secure Sockets Layer (SSL) or Transport Layer Security (TLS) with certificate verification to connect to your RDS DB instances or Multi-AZ DB clusters, consider using the new CA certificate rds-ca-rsa2048-g1. If you currently do not use SSL/TLS with certificate verification, you might still have an expired CA certificate and must update them to a new CA certificate if you plan to use SSL/TLS with certificate verification to connect to your RDS databases.
Amazon RDS provides new CA certificates as an Amazon security best practice. For information about the new certificates and the supported Amazon Regions, see Using SSL/TLS to encrypt a connection to a DB instance or cluster .
To update the CA certificate for your database, use the following methods:
Before you update your DB instances or Multi-AZ DB clusters to use the new CA certificate, make sure that you update your clients or applications connecting to your RDS databases.
Considerations for rotating certificates
Consider the following situations before rotating your certificate:
-
Amazon RDS Proxy uses certificates from the Amazon Certificate Manager (ACM). If you're using RDS Proxy, when you rotate your SSL/TLS certificate, you don't need to update applications that use RDS Proxy connections. For more information, see Using TLS/SSL with RDS Proxy .
-
If you're using a Go version 1.15 application with a DB instance or Multi-AZ DB cluster that was created or updated to the rds-ca-2019 certificate prior to July 28, 2020, you must update the certificate again. Update the certificate to rds-ca-rsa2048-g1.
Use the
modify-db-instancecommand for a DB instance, or themodify-db-clustercommand for a Multi-AZ DB cluster, using the new CA certificate identifier. You can find the CAs that are available for a specific DB engine and DB engine version using thedescribe-db-engine-versionscommand.If you created your database or updated its certificate after July 28, 2020, no action is required. For more information, see Go GitHub issue #39568
.
Updating your CA certificate by modifying your DB instance or cluster
The following example updates your CA certificate from rds-ca-2019 to rds-ca-rsa2048-g1.
Update your application trust store to reduce any down time associated with updating your CA certificate. For more information about restarts associated with CA certificate rotation, see Automatic server certificate rotation .
To update your CA certificate by modifying your DB instance or cluster
-
Download the new SSL/TLS certificate as described in Using SSL/TLS to encrypt a connection to a DB instance or cluster .
-
Update your applications to use the new SSL/TLS certificate.
The methods for updating applications for new SSL/TLS certificates depend on your specific applications. Work with your application developers to update the SSL/TLS certificates for your applications.
For information about checking for SSL/TLS connections and updating applications for each DB engine, see the following topics:
-
Updating applications to connect to MariaDB instances using new SSL/TLS certificates
-
Updating applications to connect to Microsoft SQL Server DB instances using new SSL/TLS certificates
-
Updating applications to connect to MySQL DB instances using new SSL/TLS certificates
-
Updating applications to connect to Oracle DB instances using new SSL/TLS certificates
-
Updating applications to connect to PostgreSQL DB instances using new SSL/TLS certificates
For a sample script that updates a trust store for a Linux operating system, see Sample script for importing certificates into your trust store .
Note
The certificate bundle contains certificates for both the old and new CA, so you can upgrade your application safely and maintain connectivity during the transition period. If you are using the Amazon Database Migration Service to migrate a database to a DB instance or cluster , we recommend using the certificate bundle to ensure connectivity during the migration.
-
-
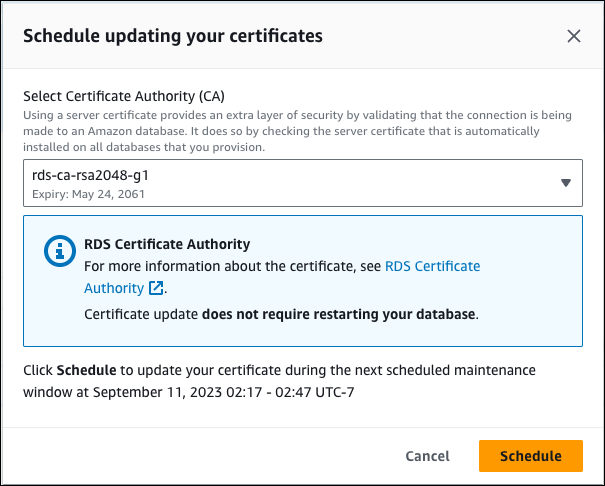
Modify the DB instance or Multi-AZ DB cluster to change the CA from rds-ca-2019 to rds-ca-rsa2048-g1. To check if your database requires a restart to update the CA certificates, use the describe-db-engine-versions command and check the
SupportsCertificateRotationWithoutRestartflag.Important
If you are experiencing connectivity issues after certificate expiry, use the apply immediately option by specifying Apply immediately in the console or by specifying the
--apply-immediatelyoption using the Amazon CLI. By default, this operation is scheduled to run during your next maintenance window.For RDS for Oracle DB instances, we recommend that you restart your Oracle DB to prevent any connection errors.
For RDS for SQL Server Multi-AZ instances with AlwaysOn or Mirroring option enabled, a failover is expected when instance is rebooted after the certificate rotation.
To set an override for your instance CA that's different from the default RDS CA, use the modify-certificates CLI command.
You can use the Amazon Web Services Management Console or the Amazon CLI to change the CA certificate from rds-ca-2019 to rds-ca-rsa2048-g1 for a DB instance or Multi-AZ DB cluster.
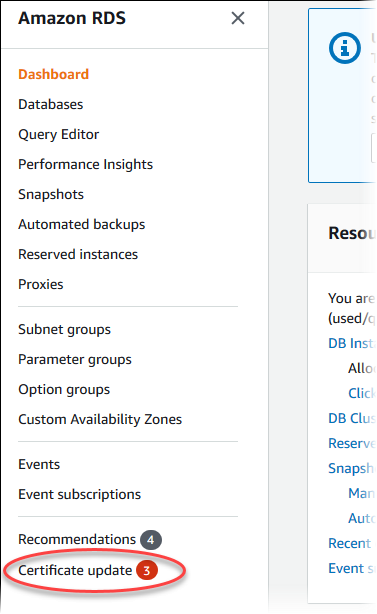
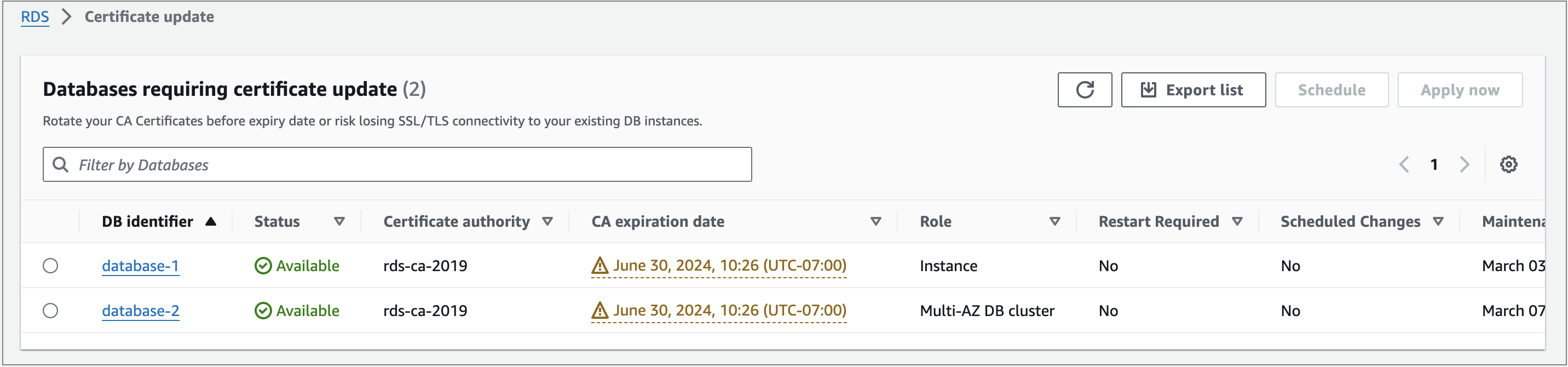
Updating your CA certificate by applying maintenance
Perform the following steps to update your CA certificate by applying maintenance.
Automatic server certificate rotation
If your root CA supports automatic server certificate rotation, RDS automatically handles the rotation of the DB server certificate. RDS uses the same root CA for this automatic rotation, so you don't need to download a new CA bundle. See Certificate authorities .
The rotation and validity of your DB server certificate depend on your DB engine:
-
If your DB engine supports rotation without restart, RDS automatically rotates the DB server certificate without requiring any action from you. RDS attempts to rotate your DB server certificate in your preferred maintenance window at the DB server certificate half life. The new DB server certificate is valid for 12 months.
-
If your DB engine doesn't support rotation without restart, Amazon RDS makes a
server-certificate-rotationPending Maintenance Action visible via Describe-pending-maintenance-actions API, at the half life of the certificate, or at least 3 months before expiry. You can apply the rotation using the apply-pending-maintenance-action API. The new DB server certificate is valid for 36 months.
Use the
describe-db-engine-versions command and inspect the
SupportsCertificateRotationWithoutRestart flag to identify
whether the DB engine version supports rotating the certificate without
restart. For more information, see Setting the CA for your database
.
Important
For Amazon RDS for Oracle DB instances, you will see the SupportsCertificateRotationWithoutRestart
flag of the DB engine versions marked as FALSE. However, Amazon RDS for Oracle DB instances do NOT
require restart, but the database listener is restarted during the server certificate rotation.
Existing database connections are unaffected, but new connections will encounter errors for a
brief period while the listener is restarted. If you want to manually rotate the server certificate,
use the
apply-pending-maintenance-action Amazon CLI command.
Sample script for importing certificates into your trust store
The following are sample shell scripts that import the certificate bundle into a trust store.
Each sample shell script uses keytool, which is part of the Java
Development Kit (JDK). For information about installing the JDK, see JDK Installation Guide