Identity-based policies and resource-based policies
A policy is an object in Amazon that, when associated with an identity or resource, defines their permissions. When you create a permissions policy to restrict access to a resource, you can choose an identity-based policy or a resource-based policy.
Identity-based policies are attached to an IAM user,
group, or role. These policies let you specify what that identity can do (its permissions).
For example, you can attach the policy to the IAM user named John, stating that he is
allowed to perform the Amazon EC2 RunInstances action. The policy could further state
that John is allowed to get items from an Amazon DynamoDB table named MyCompany. You
can also allow John to manage his own IAM security credentials. Identity-based policies can
be managed or inline.
Resource-based policies are attached to a resource. For example, you can attach resource-based policies to Amazon S3 buckets, Amazon SQS queues, VPC endpoints, Amazon Key Management Service encryption keys, and Amazon DynamoDB tables and streams. For a list of services that support resource-based policies, see Amazon services that work with IAM.
With resource-based policies, you can specify who has access to the resource and what actions they can perform on it. To learn whether principals in accounts outside of your zone of trust (trusted organization or account) have access to assume your roles, see What is IAM Access Analyzer?. Resource-based policies are inline only, not managed.
Note
Resource-based policies differ from resource-level permissions. You can attach resource-based policies directly to a resource, as described in this topic. Resource-level permissions refer to the ability to use ARNs to specify individual resources in a policy. Resource-based policies are supported only by some Amazon services. For a list of which services support resource-based policies and resource-level permissions, see Amazon services that work with IAM.
To learn how identity-based policies and resource-based policies interact within the same account, see Policy evaluation for requests within a single account.
To learn how the policies interact across accounts, see Cross-account policy evaluation logic.
To better understand these concepts, view the following figure. The administrator of the
123456789012 account attached identity-based
policies to the John, Carlos, and
Mary users. Some of the actions in these policies can be performed on
specific resources. For example, the user John can perform some actions on
Resource X. This is a resource-level
permission in an identity-based policy. The administrator also added resource-based policies to Resource X, Resource
Y, and Resource Z. Resource-based policies allow you to specify who can
access that resource. For example, the resource-based policy on Resource X allows
the John and Mary users list and read access to the
resource.
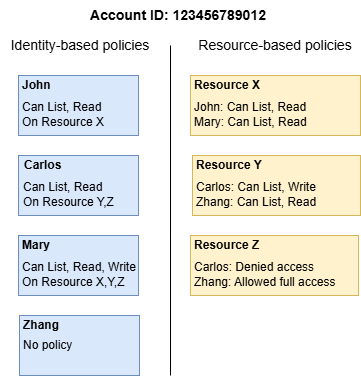
The 123456789012 account example allows the following users to perform
the listed actions:
-
John – John can perform list and read actions on
Resource X. He is granted this permission by the identity-based policy on his user and the resource-based policy onResource X. -
Carlos – Carlos can perform list, read, and write actions on
Resource Y, but is denied access toResource Z. The identity-based policy on Carlos allows him to perform list and read actions onResource Y. TheResource Yresource-based policy also allows him write permissions. However, although his identity-based policy allows him access toResource Z, theResource Zresource-based policy denies that access. An explicitDenyoverrides anAllowand his access toResource Zis denied. For more information, see Policy evaluation logic. -
Mary – Mary can perform list, read, and write operations on
Resource X,Resource Y, andResource Z. Her identity-based policy allows her more actions on more resources than the resource-based policies, but none of them deny access. -
Zhang – Zhang has full access to
Resource Z. Zhang has no identity-based policies, but theResource Zresource-based policy allows him full access to the resource. Zhang can also perform list and read actions onResource Y.
Identity-based policies and resource-based policies are both permissions policies and are
evaluated together. For a request to which only permissions policies apply, Amazon first checks
all policies for a Deny. If one exists, then the request is denied. Then Amazon
checks for each Allow. If at least one policy statement allows the action in the
request, the request is allowed. It doesn't matter whether the Allow is in the
identity-based policy or the resource-based policy.
Important
This logic applies only when the request is made within a single Amazon Web Services account. For
requests made from one account to another, the requester in Account A must
have an identity-based policy that allows them to make a request to the resource in
Account B. Also, the resource-based policy in Account B must
allow the requester in Account A to access the resource. There must be
policies in both accounts that allow the operation, otherwise the request fails. For more
information about using resource-based policies for cross-account access, see Cross account resource access in IAM.
A user who has specific permissions might request a resource that also has a permissions policy attached to it. In that case, Amazon evaluates both sets of permissions when determining whether to grant access to the resource. For information about how policies are evaluated, see Policy evaluation logic.
Note
Amazon S3 supports identity-based policies and resource-based policies (referred to as bucket policies). In addition, Amazon S3 supports a permission mechanism known as an access control list (ACL) that is independent of IAM policies and permissions. You can use IAM policies in combination with Amazon S3 ACLs. For more information, see Access Control in the Amazon Simple Storage Service User Guide.