Introducing a new console experience for Amazon WAF
You can now use the updated experience to access Amazon WAF functionality anywhere in the console. For more details, see Working with the console.
Amazon Shield
Protection against Distributed Denial of Service (DDoS) attacks is of primary importance for your internet-facing applications. When you build your application on Amazon, you can make use of protections that Amazon provides at no additional cost. Additionally, you can use the Amazon Shield Advanced managed threat protection service to improve your security posture with additional DDoS detection, mitigation, and response capabilities.
Amazon is committed to providing you with the tools, best practices, and services to help ensure high availability, security, and resiliency in your defense against bad actors on the internet. This guide is provided to help IT decision makers and security engineers understand how to use Shield and Shield Advanced to better protect their applications from DDoS attacks and other external threats.
When you build your application on Amazon, you receive automatic protection by Amazon against common volumetric DDoS attack vectors, like UDP reflection attacks and TCP SYN floods. You can leverage these protections to ensure the availability of the applications that you run on Amazon by designing and configuring your architecture for DDoS resiliency.
This guide provides recommendations that can help you design, create, and configure your application architectures for DDoS resiliency. Applications that adhere to the best practices provided in this guide can benefit from an improved continuity of availability when they are targeted by larger DDoS attacks and by wider ranges of DDoS attack vectors. Additionally, this guide shows you how to use Shield Advanced to implement an optimized DDoS protection posture for your critical applications. These include applications for which you've guaranteed a certain level of availability to your customers and those that require operational support from Amazon during DDoS events.
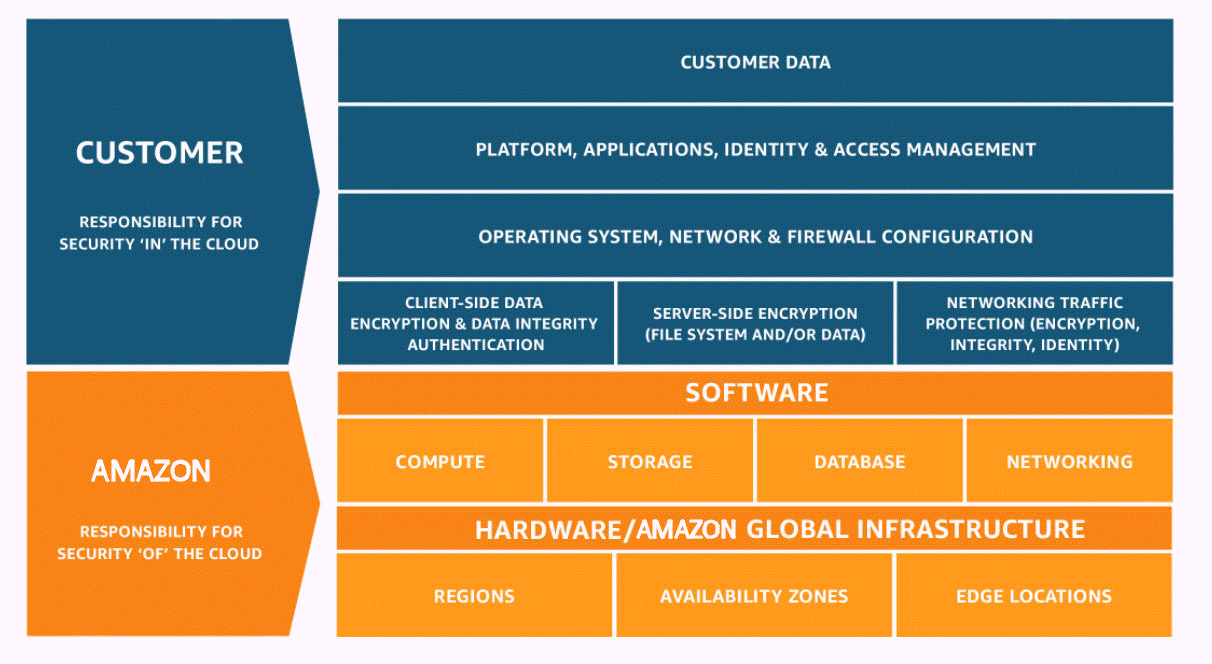
Security is a shared responsibility between Amazon and you. The shared
responsibility model
-
Security of the cloud – Amazon is responsible for protecting the infrastructure that runs Amazon services in the Amazon Web Services Cloud. Amazon also provides you with services that you can use securely. The effectiveness of our security is regularly tested and verified by third-party auditors as part of the Amazon compliance programs
. To learn about the compliance programs that apply to Shield Advanced, see Amazon Services in Scope by Compliance Program . -
Security in the cloud – Your responsibility is determined by the Amazon service that you use. You are also responsible for other factors including the sensitivity of your data, your organization’s requirements, and applicable laws and regulations.